Even on the day the Strong Customer Authentication (SCA) regulation came into force across Europe, the requirements for merchants remained unclear. The impact will be significantly differing payment experience across Europe, with increased friction in the payment process resulting in reduced conversion rates, says Paul Davidson, banking and payments solutions consultant of ERA.
T: How would you describe the impact of the Strong Customer Authentication (SCA)  directive on the ecommerce?
directive on the ecommerce?
P: Research indicates that just 40% of UK merchants are confident of being ready for SCA according to Stripe and 451 Research, and UK Finance revealing 75% of merchants across Europe were unaware of the requirements just two months before the deadline.
Merchants are likely to see a degree of loss of control over the customer payment process at the end of online purchases, as it is the card issuer who has final say on whether to trigger full SCA (step-up), what method(s) of authentication they will allow and what that authentication user experience is.
As a result, they may struggle to maintain seamless shopping and payment experiences – and some merchants may even see an extra authentication step in the payments process result in a sales drop.
T: What’s the rationale behind implementing the SCA policy? How would it change the way marketplace merchants and retailers trade? How would it change the way consumers shop?
P: The rationale behind implementing SCA is to make online payments simpler and more secure, reducing fraud in the process. The additional layer of security for online payments will make it harder for fraudulent transactions to take place if a card is compromised.
The new version of 3D Secure (3DS2), which is the card industry’s default SCA compliance tool, is designed to provide a mobile-friendly payment experience – as mobile payments today represent a significant proportion of global e-commerce – including biometric authentication methods.
Merchants will need to prepare for the new requirements by introducing payments systems that can handle the greater level of data to enable authentication stipulated by SCA. Once we pass the enforcement dates, transactions that are not appropriately coded and referred as per SCA guidelines are likely to be automatically declined by the cardholder’s bank.
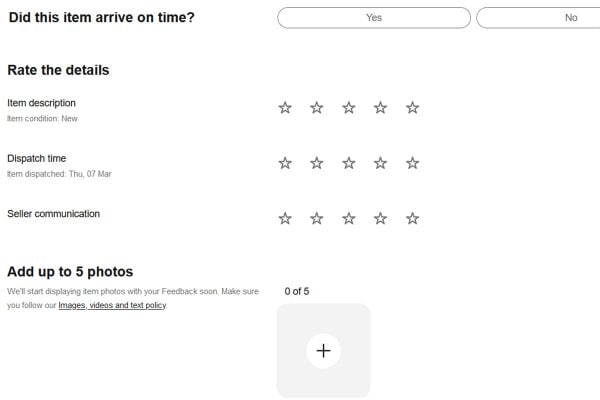
From the consumer’s viewpoint, they will experience an additional authentication step for transactions that trigger full SCA, which could create extra friction in the shopping and payments experience that is today expected to be seamless. However, as each country in Europe is now free to set different enforcement dates and favour different authentication methods, the consumer confusion may result in a higher percentage of abandoned purchases and online shopping carts, which is currently estimated to sit at a rate of 69%.
T: How does the SCA policy aim to reduce fraud and make payments more secure?
P: The SCA directive aims to reduce payment fraud by introducing two-factor authentication for ecommerce transactions.
More specifically, it introduces authentication via two of three potential authentication types – something a consumer owns, such as a phone, something they know, a PIN or password and who they are – biometric information – fingerprints, location or facial recognition), ultimately further safeguarding online payments against fraud.
The industry-preferred default solution – 3D Secure v2 – supports up to 10 times the data transmission of previous versions, so fraud risk can be better assessed to reduce false positives.
Card-based fraud is currently estimated to cost £671.4 million per year in the UK, so there is great potential to achieve significant savings for marketplace merchants, retailers and consumers through fraud prevention.
T: What’s the difference between ‘customer-initiated’ and ‘merchant-initiated’ online payments?
P: ‘Customer-initiated purchases’ are one-off transactions on ecommerce sites covering card payments and bank transfers. These will require SCA.
‘Merchant-initiated Transactions’ (MITs) typically consist of recurring subscriptions or regular direct debits and will not require SCA except for the initial payment.
The regulation allows several exemptions to require authentication for customer-initiated transactions. The Low-Risk exemption is likely to be most used where Transaction Risk Analysis (TRA) is carried out in real-time.
Currently, most merchants’ systems provide insufficient data for TRA to be carried out and upgrading to later versions of 3D Secure2 is recommended as soon as possible. Some exemptions are currently ineffective, such as Corporate payments (due to the messaging indicating that a transaction is B2B not passing through the processing systems) and Whitelisting (only American Express have developed this solution at present).
Merchants with existing MIT relationships with their customers should ensure that their payments providers have completed the processes necessary to ‘grandfather’ these, to avoid SCA being required to effectively create a new MIT after 14 September 2019.
T: How would marketplace merchants and retailers benefit from the SCA implementation?
P: Whether trading on eBay, Amazon, Alibaba or another provider, merchants benefit from the payment systems operated by the marketplace. The marketplaces, therefore, take care of the SCA requirements and have the market presence to ensure their needs are catered for within the regulation.
Previously, Amazon has famously insisted that their risk management systems out-performed 3DS1, so retailers may wonder whether the new regulation will bring them additional benefits.
One key opportunity is likely to be the ‘Whitelisting’ exemption. Once developed, cardholders will be able to use their banking apps to exempt transactions from trusted merchants from SCA. We expect that cardholders will be more likely to whitelist Amazon than a small retailer’s own website.
Other benefits will be industry-wide, such as reduced ecommerce fraud rates and reinforced trust between consumers and retailers.
Many banks started rolling out 2-factor authentication before September. Typically these used one time passwords (OTPs) sent via SMS. This solution is far from ideal as SMS was never designed to be a secure communication system, and at least one significant data breach has already resulted from its use by a bank.
Beyond this, a significant proportion of the UK population, estimated at 2 million, do not have access to digital communications at any time. Long-established banking relationships also mean that many banks do not hold current contact details for customers.
Achieving secure 2-factor authentication for these customers is a significant challenge which may not be fully resolved within the 18-month phase-in timeline in the UK.